
Introduction
Security and compliance teams at fast-growing SaaS companies are under constant pressure. Whether it’s a SOC 2 audit, HIPAA documentation, or staying updated with GDPR regulations, the compliance burden keeps growing—while the margin for error keeps shrinking.
Despite having robust DevSecOps practices and cloud security tools in place, many teams still rely on spreadsheets, ticketing tools, and frantic last-minute scrambling. But there’s a smarter way forward: MCP agents.
In this blog, we’ll explore how MCP agents are transforming the way security teams approach compliance automation, reducing manual effort, and enabling audit-ready reporting for frameworks like SOC 2, HIPAA, and GDPR.
What Are MCP Agents? A New Era for Compliance Automation
Inside your system, MCP (Managed Compliance Pipeline) agents are tiny, custom-written services or scripts.Their goal is to continuously monitor, verify, and report on compliance posture; audits are not the only use for them.
These agents work along with your cloud platforms, code repositories, CI/CD pipelines, and infrastructure to:
- Automatically gather evidence (access records, logs, and configurations)
- Enforce security policies and compliance rules
- Generate real-time reports aligned with compliance frameworks
To put it briefly, MCP agents automate and add intelligence to a process that has historically been reactive and heavily manual.
Why Many SaaS Companies Still Have Issues with Compliance Reporting
You’re not alone if you still use Jira tickets and spreadsheets to manage your SOC 2 reporting or HIPAA compliance documentation. Here’s why so many teams continue to have difficulties:
- Systems that are siloed: Security information is dispersed throughout AWS, GitHub, Okta, and Jira.
- Manual reporting: Obtaining logs, taking screenshots, and formatting documentation may take many days or weeks.
- Human error: Manual checklists are prone to errors and are difficult to manage.
- Lack of continuous visibility: You’re either audit-ready or scrambling to get there.
And yet, all of these problems are solvable—with the right automation strategy.
How MCP Agents Automate SOC 2, HIPAA, and GDPR Compliance Reporting
Let’s break down what MCP agents actually automate when it comes to popular compliance frameworks:
✅ SOC 2 Compliance Automation
- Access control, audit recording, and incident response preparedness are all continuously monitored.
- Real-time validation of security controls mapped to SOC 2 Trust Principles.
- Automated evidence collection for security, availability, and confidentiality controls.
✅ HIPAA Compliance Automation Tools
- Monitoring and warning about data encryption while it’s in transit and at rest.
- keeping an eye on technological, administrative, and physical protections.
- Creating HIPAA paperwork that includes access histories and audit-traceable logs.
✅ GDPR Report Generation Automation
- Data subject access and deletion request logging.
- Real-time alerts for unauthorized access or data breaches.
- Reporting across data handling practices and storage policies.
Security teams can transition from reactive audits to always-on compliance by deploying MCP agents. This proactive strategy significantly lessens audit fatigue and enhances security posture.
Security Compliance for SaaS Companies: From Chaos to Control
For SaaS companies scaling fast, every audit cycle can feel like a bottleneck. Engineers are pulled off product work to gather documentation. Security teams are swamped with data wrangling. Deadlines loom. Tension builds.
MCP agents shift the narrative. Instead of sprinting toward compliance, you’re operating in a compliant state, all the time.
And the benefits don’t stop there:
- Reduced engineering effort: Minimal disruption to development cycles.
- Improved audit speed: Weeks of prep condensed into hours.
- Greater visibility: Continuous dashboards for compliance health.
DevSecOps + Compliance Automation = Scalable Governance
Code quality, test coverage, and deployment pipelines are already enforced by automation in contemporary DevSecOps systems. What is causing compliance to remain trapped in the past, then?
You can enforce compliance requirements at the same degree of automation by incorporating MCP agents into your CI/CD workflows, guaranteeing secure, compliant releases by default.
For example:
- Blocking deploys that violate encryption policies.
- Automatically flagging access changes.
- Generating changelogs that double as audit evidence.
The result? Security compliance becomes a natural extension of your development process, not a disruption to it.
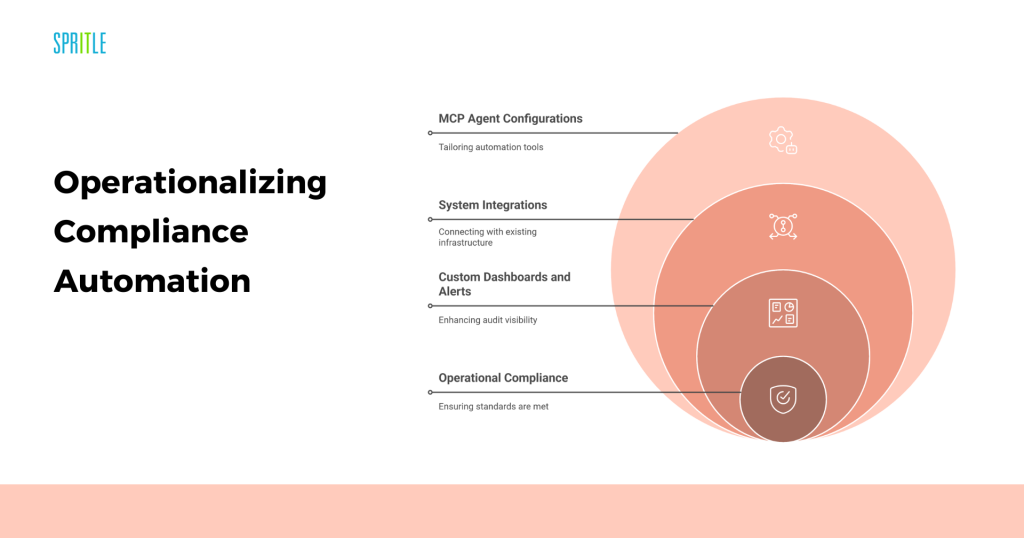
Why Spritle? Operationalizing Compliance Automation with Expertise
Let’s be honest: even the most powerful automation tools don’t work without proper implementation. While MCP agents offer incredible potential, they’re not “plug and play.” Success depends on understanding your tech stack, mapping your controls, and setting up integrations the right way.
That’s where Spritle Software steps in—not just as a tool provider, but as a strategic implementation partner.
We help security and DevOps teams:
- Identify the right MCP agent configurations.
- Integrate with cloud, identity, and version control systems.
- Create personalized alerts and dashboards to increase audit visibility.
- Verify that controls adhere to GDPR, HIPAA, and SOC 2 requirements.
We are not here to sell you software; we help you operationalize the tools you already have.
Final Thoughts: Is Your Team Ready for Always-On Compliance?
The landscape of security compliance is changing.
Spreadsheet checklists, manual audits, and disorganized paperwork are being replaced with intelligent, ongoing systems.
Perhaps it’s time to ask why compliance is still being handled the hard way if your team continues to view it as a quarterly crisis rather than a continuous capacity.
Your team may move from firefighting to foresight, from reactive to proactive, with the help of MCP agents, who provide a more intelligent way forward.
Spritle Software is available to assist in facilitating that transition in a seamless, scalable, and secure manner.
