Healthcare organizations may have technology and procedures in place to prevent data theft, but it’s difficult for organizations to find every security weakness.
To help protect our network and electronic patient health information (PHI), we need to examine your environment the way a hacker would. Ethical hacking or penetration testing is the art of analyzing network environments, identifying potential vulnerabilities, and trying to exploit those vulnerabilities just like a hacker would. The difference is that these people are on our side.
Penetration testing is vital for our security and can help in reaching Health Insurance Portability and Accountability Act (HIPPA) compliance.
In this white paper, you will learn the basics of penetration testing, best practices to prepare for a penetration test, and the cost of penetration testing.

Penetration Test:
Pen Test is the most commonly used security testing technique for web applications.
Healthcare Web application Penetration Testing is done by simulating unauthorized attacks internally or externally to get access to sensitive data.
A web penetration helps the tester to find out the possibility of scenarios to access the data from the internet, find about the security of their email servers and also get to know how secure the web hosting site and server are.
Importance of Pen Test:
- Identify and prioritize security risks
- Intelligently manage vulnerabilities
- Leverage a protective security approach
- Verify existing security programs are working and discover your security strengths
- Increase confidence in your security strategy
- Meet regulatory requirements
Stages of Pen Test:
Planning and Preparation (Before Testing):
- Scope definition
- Availability of documentation to testers
- Determining the success criteria
- Reviewing the test results from the previous testing
- Understanding the environment
Attacks/Execution Phase (During Testing):
- Ensure to run a test with different user roles
- Awareness on how to handle Post-Exploitation
- Generation of test reports
Post Execution Phase (After Testing):
- Suggest remediation
- Retest vulnerabilities
- Cleanup
Types of Pen Test:
- Web Application Tests
- Network Security Tests
- Cloud Security Tests
- IoT Security Tests
- Social Engineering
Web Penetration Testing Methodology:
To know more about each methodology, you can visit the link:
- OWASP (Open Web Application Security Project)
- OSSTMM (Open Source Security Testing Methodology Manual)
- PTF (Penetration Testing Framework)
- ISSAF (Information Systems Security Assessment Framework)
- PCI DSS (Payment Card Industry Data Security Standard)
Web Penetration Testing Scenario’s:
To know more about each scenario’s of pen test, you can visit the link :
- Cross Site Scripting
- SQL Injection
- Broken authentication and session management
- File Upload Flaws
- Caching Servers Attacks
- Security Misconfigurations
- Cross-Site Request Forgery
- Password Cracking
Role & Responsibilities of Penetration Testers:
- Testers should collect required information from the organization to enable penetration tests
- Find flaws that could allow hackers to attack a target machine
- Pen Testers should think & act like real hackers albeit ethically.
- Work done by penetration testers should be reproducible so that it will be easy for developers to fix it
- Start date and end date of test execution should be defined in advance.
- A tester should be responsible for any loss in the system or information during the Software Testing
- A tester should keep data and information confidential
Top Penetration Testing Tools in Market:
- Zed Attack Proxy (ZAP)
- Wfuzz
- Wapiti
- W3af
- SQLMap
- SonarQube
- Nogotofail
- Iron Wasp
- Grabber
- Arachni
Here I will discuss about the OWASP ZAP tool and its features
OWASP Testing Methodology with ZAP tool:
The Open Web Application Security Project (OWASP) is an open, online community that creates methodologies, tools, technologies and guidance on how to deliver secure web applications. It is an international collaborative initiative comprised of both individuals and corporations. The project aims to standardize security approaches in web development and spread associated knowledge.
OWASP ZAP (ZAP) is one of the world’s most popular free security tools and is actively maintained by hundreds of international volunteers. It can help to find security vulnerabilities in web applications. It is also a great tool for experienced pen testers and beginners
Why we chose ZAP?
ZAP is a free open-source tool which is easy to setup and use. As it is used by the wider community, there is a lot of help available in online to help you setup and use the tool.
ZAP is cross platform i.e. you can install it in Windows, Linux or Mac OS.
ZAP can be run in a Docker Container, which suited our project tech stack. Also, its functionality is scalable with many diverse extensions published on GitHub.
ZAP Jenkins Plugin can be setup to run the scans as part of CI / CD pipelines.
How it works?
ZAP is what is known as a “man-in-the-middle proxy“. It stands between the browser and the web application. While you navigate through all the features of the website, it captures all actions. Then it attacks the website with known techniques to find security vulnerabilities.
As ZAP spiders the web application, it constructs a map of the web applications’ pages and the resources used to render those pages. Then it records the requests and responses sent to each page and creates alerts if there is something potentially wrong with a request or response.
Launch ZAP tool:
In order to perform web application security testing to discover vulnerabilities, we launch ZAP tool which is installed in the machine. Here I installed ZAP 2.9.0 version.
Once launched this is initial screen for the ZAP tool. You can see that features like Automated Scan and Manual Explore.

Automated Scan:
This option allows you to launch an automated scan against an application just by entering the URL.
Here I used this URL: demo.hospitalrun.io/ for automated scan.
To run a Quick Start Automated Scan:
- Start Zap and click the large ‘Automated Scan’ button in the ‘Quick Start‘ tab.
- Enter the full URL “demo.hospitalrun.io/“of the web application you want to attack in the ‘URL to attack’ text box.
- Click the ‘Attack‘ button.

To view the alerts created during your test:
- Click the Alerts tab in the Information Window.
- Click each alert displayed in that window to display the URL and the vulnerability detected in the right side of the Information Window.
- In the Workspace Windows, click the Response tab to see the contents of the header and body of the response. The part of the response that generated the alert will be highlighted.

Manual Explore Scan:
Spiders are a great way to explore the basic site, but they should be combined with manual exploration to be more effective. This functionality is very useful when your web application needs a login or contains things like registration forms, etc.
You can launch browsers that are pre-configured to proxy through ZAP via the Quick Start tab. Browsers launched in this way will also ignore any certificate validation warnings that would otherwise be reported.

To Manually Explore the web application:
- Start ZAP and click on the large ‘Manual Explore‘ button in the Quick Start tab.
- Enter the full URL “demo.hospitalrun.io/“of the web application to be explored in the ‘URL to explore’ text box.
- Select the browser you would like to use and click the ‘Launch Browser‘ button.
This will launch the selected browser with a new profile. Now explore all of the targeted web applications through this browser. ZAP passively scans all the requests and responses made during your exploration for vulnerabilities, continues to build the site tree, and records alerts for potential vulnerabilities found during the exploration.
Passive Scanning:
Passive scans only scan the web application responses without altering them. It does not attack or insert malicious scripts to the web application, so this is a safe scan; you can use it if you are new to security testing. Passive scanning is good at finding some vulnerabilities and as a way to get a feel for the basic security of a web application.
Active Scanning:
Active scan attacks the web application using known techniques to find vulnerabilities. This is a real attack that attempts to modify data and insert malicious scripts in the web application.
“Active scans put the application at risk, so do not use active scanning against web applications you do not have permission to test.”
Inspecting the test results:

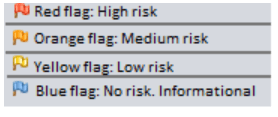
Once the scan is completed, ZAP generates a list of issues that are found during the scan. These issues can be seen on the Alerts tab that is located in the bottom pane. All the issues are marked with color coded flags.
You can also generate an multiple report through the ‘Report’ menu option on the top of the screen.
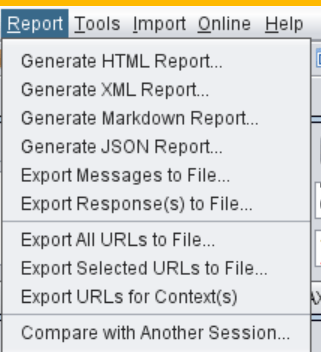
Here I attached HTML report image for reference.

Penetration Testing Certifications:
To know more about each certifications, you can visit the link:
- OSWE (Offensive Security Web Expert)
- GWAPT (GIAC Web Application Penetration Tester)
- CWAPT (Certified Web App Penetration Tester)
- eWPT (elearnSecurity Web Application Penetration Tester)
In today’s world technology, the healthcare industry has consistently been one of the top targets for hackers and cybercriminals over the past several years. In fact, in a recent study by Ponemon, almost 90% of healthcare organizations had experienced a data breach in the past two years, and a whopping 45% have experienced five or more data breaches in the same period of time.
So, In our developing “Functional Medicine Healthcare Application” will plan to do the pen test by considering “HIPPA Privacy Rule“. The HIPAA Privacy Rule protects the privacy of individually identifiable health information, called protected health information (PHI) .
At the end, We should make sure that our healthcare application is fully protected and there is no way to hack or destruct our application.
